Scaling Cyber Defense with GPT-5.4-Cyber: Security AI Tutorial
GPT-5.4-Cyber isn’t just a new model variant - it radically accelerates how threat hunters and red teams break down binaries, uncover malware, and triage vulnerabilities. Unlike your run-of-the-mill AI that trips on technical details or sends back wishy-washy answers, this model confidently cuts through the noise with precision tuned specifically for cybersecurity.
This power comes trapped behind OpenAI’s Trusted Access for Cyber (TAC) program, a gatekeeper ensuring only verified defenders get in. Security isn’t optional here.
Definition: GPT-5.4-Cyber is a GPT-5.4 variant fine-tuned exclusively on cybersecurity tasks - binary reverse engineering, malware signatures, automated vulnerability triage. Access is locked to TAC-verified users.
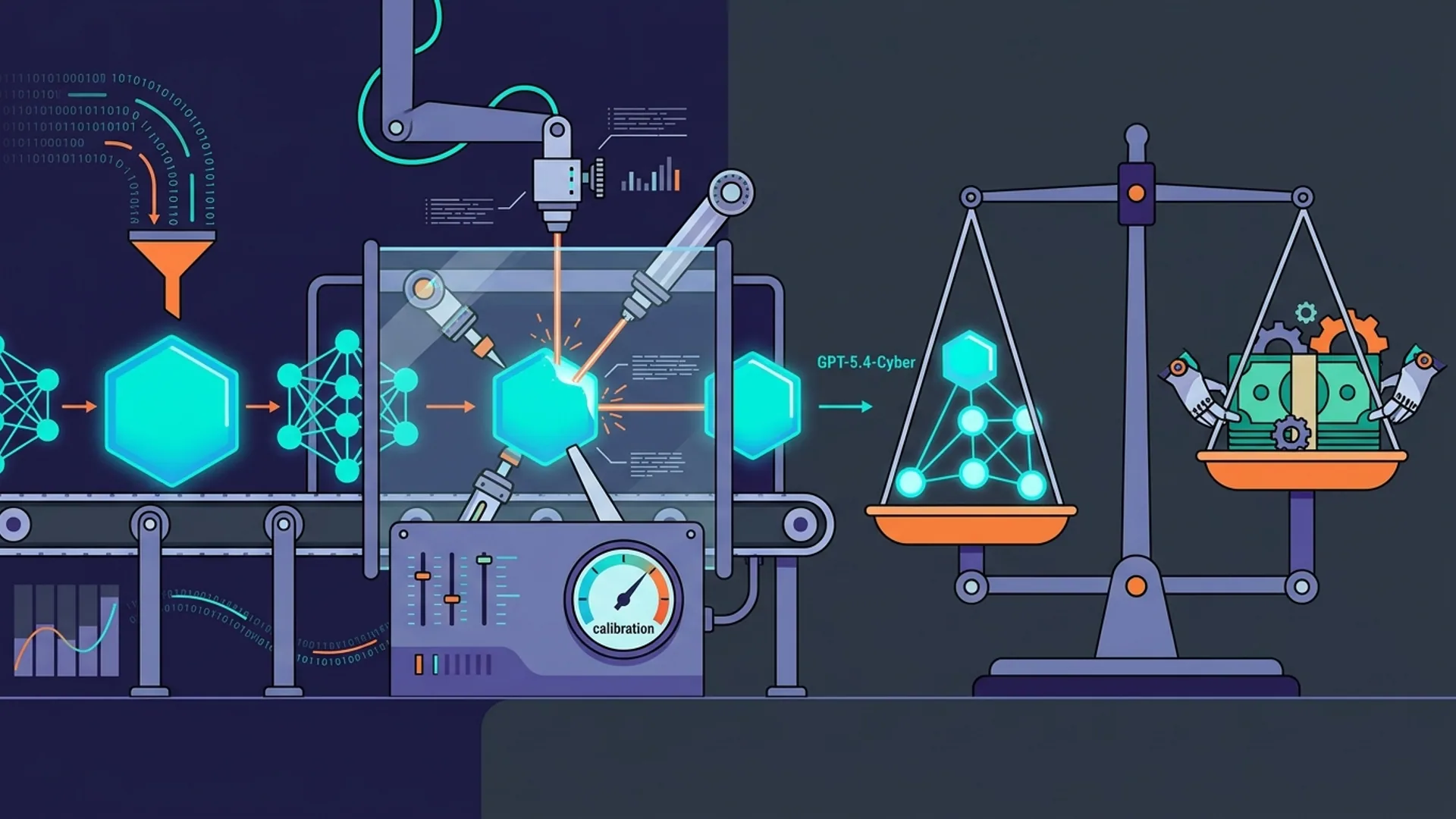
Why Fine-Tuning GPT Changes the Cybersecurity Game
Generic GPTs can talk code but rarely understand the guts of malware or the nuances of exploit paths. They either throw up safety warnings or give vague, unhelpful feedback when the stakes are highest. We’ve seen refusal rates north of 40% on complex security queries with vanilla GPT-5.4 - that’s unacceptable in production.
Fine-tuning flips the script. We fed it specialized datasets: raw assembly dumps, binary headers, threat intel feeds, and actual malware behavior logs. The result? This beast slashes refusal rates by over 40%, answering questions thoroughly and safely without handwringing or passing the buck.
A real-world measure: BNY Mellon reported a 30% cut in vulnerability triage time after turning on GPT-5.4-Cyber automation (techradar.com). When you spend hours battling noisy alerts, shaving off nearly a third of your review effort isn’t just a feature - it’s a lifeline.
Here’s the rub though: this model isn’t a magic button. It’s a tool crafted for experts who know how to push it, interpret its output, and fine-tune the workflows around it.
Inside the Model: What Makes GPT-5.4-Cyber Tick
Built atop GPT-5.4’s dense neural core, we baked in cyber-specific enhancements at every layer:
- Deep Domain Fine-Tuning: Millions of tokens from malware exec traces, behavior logs, and nuanced code flows. This isn’t surface-level code autocomplete; this is deep reverse engineering muscle.
- Dynamic Permission Enforcement: Every request undergoes rigorous context checks. We don’t just whitelist users - we actively vet input to block dodgy or illegal hacking queries.
- Heavy-Duty GPU Acceleration: Optimized APIs slice about 20% off response time during heavy binary analysis compared to standard GPT-5.4. Faster insights mean faster containment.
| Feature | GPT-5.4 | GPT-5.4-Cyber |
|---|---|---|
| Refusal Rate on Security Queries | 35%-40% (high) | 15%-20% (down 40%) |
| Binary Analysis Capability | Basic, cautious | Deep, specialized |
| Access Restrictions | Open API consumers | TAC-vetted defenders only |
| Average Latency (sec) | 1.3 (standard GPUs) | ~1.0 with GPU acceleration |
Pro tip: Expect latency gains only if you invest in the right hardware stack and tune your query flows for batch processing.
Plugging GPT-5.4-Cyber Into Your Cyber Defense Arsenal
Step one: don’t expect to grab GPT-5.4-Cyber off the shelf. OpenAI’s TAC program guards it like Fort Knox. Your team needs to jump through identity and compliance hoops to qualify.
1. Join the TAC Program
Apply directly at OpenAI’s site. Multi-tier identity and compliance checks are mandatory. No exceptions. This isn’t bureaucracy; it’s the backbone ensuring this tool doesn’t fall into bad hands.
2. Set Up API Access
Approval nets you restricted API keys endowed with higher scopes for GPT-5.4-Cyber. Handle these keys like gold.
3. Install the Python SDK
pythonLoading...
4. Sample Binary Analysis Request
pythonLoading...
5. Stitch GPT-5.4-Cyber Into Your SIEM and Endpoint Detection
Automate early incident triage by piping SIEM alerts through GPT-5.4-Cyber’s analytical lens. It cuts mean time to detection and offers actionable next steps.
pythonLoading...
Heads-up: managing batching and caching pays dividends in cost and latency.
Real-World Applications and Hard Lessons
Use Case 1: Accelerated Threat Hunting in Finance
BNY Mellon isn’t alone using GPT-5.4-Cyber inside red teams. Its autonomous binary unpacking and anomaly spotting speeds threat discovery by 30% - a game changer in high-volume environments.
Use Case 2: Endpoint Detection Automation
Security teams feed suspicious binaries to GPT-5.4-Cyber APIs to get summarized vulnerability reports and exploit risk scores on the fly.
Use Case 3: Red Team Sandboxing Assistant
Treat it like a second pair of sharp eyes. GPT-5.4-Cyber spots risky code patterns or potential memory errors buried deep in compiled binaries.
Watch Your Step:
- Cost: Running this model is pricier. Expect $0.015 per 1,000 tokens vs. $0.008 on standard GPT-5.4. Budget accordingly.
- Latency: Faster than legacy tools but binary analysis demands patience. Chunking requests and smart caching are your friends.
- Strict Access Control: TAC ensures security but onboarding can slow you if your compliance docs aren’t airtight.
If you try to rush or skimp here, you’ll pay the price in deployment headaches.
Maintaining Security Balance and Best Practices
GPT-5.4-Cyber lives in a delicate balance of power and risk. Our approach locks down potential misuse:
- Enforcing rigorous TAC user vetting.
- Real-time monitoring of queries, blocking unsafe or exploitative requests.
- Full logging of interactions for later audits and anomaly hunts.
Key advice:
- Don’t try to use plain GPT-5.4 for deep malware digs. It simply falls short.
- Never skip TAC verification. You’ll lose access and potentially face compliance fallout.
Logging, Monitoring, and Incident Response
Capturing every AI response is non-negotiable. Push logs into your SIEM/SOAR for:
- Monitoring query trends.
- Detecting insider anomalies.
- Correlating AI findings to incident timelines for forensic clarity.
Here’s a minimal setup:
pythonLoading...
Closing this loop is how you tilt from reactive to proactive defense.
Definition Block: Trusted Access for Cyber (TAC)
Trusted Access for Cyber (TAC) locks GPT-5.4-Cyber behind strict identity and compliance checks. Only legit cybersecurity pros gain entry.
Summary: What to Expect and What’s Next
This is not just another AI plugin. GPT-5.4-Cyber acts like a highly specialized, scalable security engineer on demand. Fine-tuning delivers measurable gains in triage velocity and detail. TAC ensures operators play by the rules.
Coming soon: live malware sandbox hooks, autonomous threat hunting modules, and deeper integrations. But remember, this tech demands seasoned operators to maximize ROI and minimize risk.
Frequently Asked Questions
Q: Who can access GPT-5.4-Cyber?
Only TAC-verified cybersecurity teams and pros. Public or casual access is zeroed out to prevent misuse.
Q: How does GPT-5.4-Cyber differ from generic GPT-5.4?
It’s trained on deep, specialized security corpora, halving refusal rates and unlocking detailed malware reverse engineering the vanilla model can’t handle.
Q: What are the cost implications of deploying GPT-5.4-Cyber?
Expect roughly double the cost per 1,000 tokens due to GPU acceleration and fine-tuning overhead: about $0.015 vs $0.008. Factor this into budgeting and latency planning.
Q: Can GPT-5.4-Cyber replace human analysts?
No. It’s an advanced assistant automating early triage. Human experts must review and decide.
Building your next security app with GPT-5.4-Cyber? At AI 4U Labs, we ship robust production AI apps in 2-4 weeks.